
Subscriber management is very important in fixed wireless access networks. Devices such as the MME, BNG, and CPE help operators manage who can use the network. These devices also help deliver services to users. FWA now makes up almost 9% of all broadband connections in the world. Good authentication and subscriber management stop people from getting in without permission. They also make the network safer. These steps help keep service quality high. This is important because FWA users want more bandwidth. Operators use these systems to give every subscriber a good and steady experience.
Key Takeaways
- Subscriber management is very important. It helps control who can use fixed wireless networks. It also makes sure the service works well.
- A subscriber database keeps user information. This helps operators manage services. It also helps them watch how much people use the network.
- Policy control systems make rules for bandwidth and data limits. These rules stop the network from getting too busy. They also make sure everyone gets a fair chance to use it.
- Provisioning systems make it easy to add new subscribers. They help start new services fast.
- SIM-based authentication is used a lot. It is safe and easy for users. Devices can connect without using passwords.
- Certificate-based authentication gives strong security. Each device gets its own digital identity.
- Operators should update their authentication systems often. This helps protect against new security problems.
- Automation and AI can make subscriber management better. They can guess network traffic. They can also find problems before users notice them.
Subscriber Management in Fixed Wireless Access

Definition and Role
Subscriber management in fixed wireless access helps operators decide who can use the network. It also controls what services each person gets. Only people with permission can connect to the network. Operators use subscriber management to give out internet services. They also keep the network working well and safe from threats. The system gives authentication information to important network parts like the Mobility Management Entity (MME) and the Broadband Network Gateway (BNG). This way, the process is similar to what fixed networks use. Subscriber management helps home and business users get a steady internet connection.
Key Components
Subscriber Database
The subscriber database keeps important details about each user. It stores things like identity, service plans, and authentication credentials. The database is the main place to check users when they try to join the network. It lets operators see how much each person uses and set the right rules for them.
Policy Control
Policy control systems pick what kind of service each subscriber gets. These systems set rules for bandwidth, data limits, and when people can use the network. Policy control helps operators handle lots of data use and stop the network from getting too busy. It also keeps the network safe from bad or fake traffic by using security policies.
Provisioning Systems
Provisioning systems help set up new subscribers and turn on their services. These systems make it easy to add users to the network. They make sure each subscriber gets the right settings and access. Provisioning systems also let operators quickly help customers and change service plans.
Note: Operators have some problems with subscriber management. They must deal with lots of data use, stop bad traffic, and keep the network safe. They also need to give fast, smooth internet in many places.
| Network Element | Role in Subscriber Management |
|---|---|
| Cell Tower | Helps users talk to the network and links to the Internet backbone. |
| Customer Premises Equipment | Connects users to the network and sends and gets data for Internet use. |
| Network Backbone | Moves lots of data between the cell tower and the main Internet. |
| SIM Card | Lets devices use secure authentication and get on the network with cellular technology. |
Importance for Service Quality
Subscriber management is important for keeping service quality high and controlling who gets on the network. Operators use it to make sure every user has a steady connection and good service. The system stops people without permission and identity spoofing, which can hurt the network. By giving authentication information to the MME, subscriber management makes sure only real users connect. The process has a few steps:
- The MME sends an Authentication Request to the Home Subscriber Server (HSS) with the user’s identity and network ID.
- The HSS uses a secret key to make authentication vectors.
- The MME gets an Authentication Response with tokens to check the user.
These steps help operators give steady and reliable connections, even as they work with 5G and build new network parts. Subscriber management helps keep service quality the same, which is very important for home and business users in fixed wireless access networks.
Authentication Methods in FWA Networks
SIM-Based Authentication
SIM-based authentication is used a lot in fixed wireless access. Operators like this method because it is safe and easy for users. The SIM card holds special information about the subscriber. When a device wants to join, the network checks this information. This makes sure only real users can get on the network. It helps keep the network safe and lets only real people use fast internet.
The table below shows how SIM-based authentication works in fixed wireless access:
| Component/Process | Description |
|---|---|
| EAP-SIM/AKA Authentication | Uses the SIM card to securely verify devices connecting to the network. |
| 3GPP AAA Server | Handles authentication, authorization, and policy enforcement. |
| Cryptographic Key Generation | Creates keys for encrypting data during the connection. |
Operators pick SIM-based authentication because it is always ready. The process happens by itself and users do not need to remember passwords. The network checks the SIM card and lets the user in if the details match. This method also helps with policy enforcement and routing. It makes sure each subscriber gets the right service and stays online.
Certificate-Based Authentication
Certificate-based authentication is another way to keep fixed wireless access safe. Operators use digital certificates to give each device its own identity. This method uses strong encryption to keep data safe and stop people from getting in without permission. Each device gets a certificate, which is like a digital ID card. The network checks this certificate before letting the device join.
The table below explains the advantages of certificate-based authentication:
| Advantage | Description |
|---|---|
| Strong Encryption | Protects data with encryption keys, making it hard for attackers to read messages. |
| Impenetrable Identification | Gives each device a unique digital identity, stopping unauthorized users. |
| Reduced Attack Surface | Removes the need for passwords, lowering the risk of attacks. |
| Elimination of Credential Theft | Keeps private keys safe on devices, stopping stolen credentials from being used. |
| Seamless User Experience | Lets users connect easily without changing passwords often. |
| Eliminating Password Reset Hassle | Reduces the need for password resets, making connections smoother. |
| Foiling Credential Theft Attempts | Stops attacks like man-in-the-middle and Evil Twin by removing password weaknesses. |
Operators like certificate-based authentication when they need strong security and high availability. This method works well for big networks and businesses. It also makes logging in fast and simple for users.
EAP and Other Protocols
The Extensible Authentication Protocol (EAP) is a flexible tool used in fixed wireless access. EAP supports many ways to check who is joining, like SIM-based and certificate-based methods. Operators use EAP because it helps keep the network safe and protects user data.
EAP helps with some important things in fixed wireless access:
- Eavesdropping: EAP helps stop people from listening to network traffic.
- Authentication and Authorization: EAP checks who users and devices are before letting them in.
- Framework for Authentication: EAP gives operators a way to use different authentication methods.
Operators often use these EAP types:
- EAP-TLS: Uses digital certificates for both the device and the network, making sure only trusted users connect.
- EAP-TTLS: Builds on EAP-TLS and allows username and password authentication inside a secure tunnel.
- EAP-PEAP: Creates a secure tunnel for password-based authentication, keeping user credentials safe.
EAP is important in fixed wireless access because it lets operators pick the best way to check users. This helps them give strong security and high availability to all subscribers.
The table below shows some of the most widely used authentication methods in fixed wireless access networks:
| Authentication Method | Description |
|---|---|
| Pre-shared key | Used for individuals, home offices, and small offices. |
| Password-based security | Common in enterprises with strong password policies. |
| Certificate-based security | Used by enterprises that need enhanced security. |
| IEEE 802.1X | Supports authentication in modern wireless networks, especially with WPA2 in enterprise mode. |
Operators use these methods to keep their networks safe and working well. They want every subscriber to have fixed wireless access with strong protection and high availability.
Implementation in FWA
Operators pick certain authentication methods in fixed wireless access. They do this to keep their networks safe and give good service. They must make sure only real users can join. This keeps the network safe and helps everyone get steady internet.
Authentication in fixed wireless access starts with the customer premises equipment, or CPE. The CPE is the main gateway for each subscriber. It sends a request to join the network. The network checks who the device is. This step is important because it blocks people who should not get in.
The Mobility Management Entity, or MME, is very important here. The MME helps with network registration and starts authentication. It checks the information from the CPE. If the details match what is in the subscriber database, the MME lets the device connect. This keeps user data safe and only lets approved devices use fast internet.
Operators use different authentication methods for their needs. SIM-based authentication is popular because it is easy for users and hard for attackers. The SIM card has secret information. When the CPE tries to join, the network uses the SIM to check if the user is real. This method works well for both mobile and fixed wireless access. It helps with quick and steady connections.
Certificate-based authentication is another option. Operators use it when they need stronger security. Each device gets a digital certificate. The network checks this certificate before letting the device in. This stops identity spoofing and keeps the network safe from attacks.
EAP and other protocols give operators more choices. They can pick what works best for their network. EAP lets them use SIM cards, certificates, or passwords. This is helpful in fixed wireless access because there are many types of users.
The table below shows why operators pick certain authentication methods in fixed wireless access:
| Authentication Method | Why Operators Choose It |
|---|---|
| SIM-Based | Easy for users, strong security, supports automation |
| Certificate-Based | Strongest security, unique device identity |
| EAP Protocols | Flexible, supports many devices and user types |
Operators want to keep their networks safe and give every user a good experience. They use these authentication methods to control who can join. This helps them give steady service, even when lots of people use the network.
Tip: Operators should check their authentication systems often. This helps them find weak spots and stay safe from new threats.
Authentication in fixed wireless access does more than stop bad actors. It also helps operators manage network resources. By knowing who is on the network, they can give each user the right amount of bandwidth. This keeps the service fair and steady for everyone.
Subscriber Lifecycle and Experience
Onboarding and Provisioning
Onboarding and provisioning are the first steps for new subscribers. Operators want this to be quick and simple. They use zero-touch onboarding and automated provisioning to help users connect fast. These tools mean people do not have to set things up by hand. This lowers mistakes and saves time for everyone.
- Zero-touch onboarding lets devices join the network by themselves.
- Automated provisioning makes user accounts and services ready right away.
- Orchestration tools turn on internet services faster.
- These systems help work go smoother and cut down wait times.
Operators pick these ways because they want every user to start easily. Fast onboarding helps people get online without trouble. This is important for homes and businesses. When users connect with no problems, they have a better experience from the start.
Policy Enforcement
Policy enforcement helps operators control how users get on the network and what they can do. This step is important because it keeps things fair and safe for all. Operators use some main parts to manage rules and make sure each subscriber gets the right service.
| Component | Description |
|---|---|
| PCRF | Decides on policy control and charging. |
| PCEF | Makes sure the PCRF’s rules are followed. |
| AF | Gives session details to the PCRF. |
| SPR | Keeps subscription and policy info for each user. |
These parts work together to handle bandwidth, data limits, and service quality. Operators use them to stop the network from getting too busy and to block misuse. Policy enforcement makes sure every subscriber gets good service and high availability.
Service Activation and Support
Service activation comes after onboarding and setting up rules. Operators turn on the services each user asks for. They also give support if there are any problems. Good support is important to keep users happy and connected.
Usage Tracking
Operators watch how much data each user uses. They do this to make sure everyone stays within their plan. Usage tracking helps find strange activity and stops abuse. It also lets operators offer different plans for different needs.
Troubleshooting
When something goes wrong, operators need to fix it fast. Troubleshooting tools help find and solve problems with connections or devices. Quick fixes keep users online and make the experience better.
Operators who focus on easy onboarding, strong policy rules, and good support give everyone a better experience. These steps help users trust the network and enjoy steady, high-quality business internet.
Enhancing Subscriber Experience
Operators want every subscriber to have a good experience. Happy subscribers stay with the service and tell friends about it. When operators manage subscribers well, they give steady and high-quality internet to homes and businesses.
A strong subscriber management system helps operators know what each user needs. They can change services to match how people use the internet. Some people need more bandwidth for video calls. Others want fast downloads. Operators use this information to make service plans that fit real needs.
Operators also use advanced platforms like vBNG Evo. This platform lets them change services when needed. It helps them give the right quality of service (QoS) to each subscriber. When the network gets busy, the system can move resources around. This way, everyone still gets a good connection. Elastic scaling means users do not notice slowdowns during busy times.
Operators who connect data from different network parts can fix problems faster. This is called service assurance. It helps them find and fix issues before users see them. It also lets them add new features or fix outages quickly.
A steady experience for all subscribers is important. When everyone gets the same good service, trust grows. Subscribers feel sure their internet will work when they need it. This trust makes people tell others and stay with the service longer.
Operators can use different ways to make the subscriber experience better:
- Personalized Service Plans: Operators look at usage data to offer plans that fit each subscriber.
- Proactive Support: They watch the network and fix problems before users ask for help.
- Clear Communication: Operators tell subscribers about changes or upgrades.
- Flexible Upgrades: They let users change plans easily as their needs grow.
| Strategy | Benefit for Subscribers |
|---|---|
| Personalized Plans | Better fit for individual needs |
| Proactive Support | Fewer disruptions and faster fixes |
| Clear Communication | Less confusion and more trust |
| Flexible Upgrades | Easy to adapt to changing demands |
Operators who focus on these things make the experience better for everyone. They build loyalty and help subscribers stay happy with their fixed wireless access service.
Security and Compliance Challenges
Threats and Vulnerabilities
Fixed wireless access networks face many dangers. These dangers can hurt network safety and make users lose trust. Operators need to know why these dangers are important. They can cause the network to stop working. They can also lead to lost data or money problems. Some common dangers are:
- Malware attacks can break things and steal data.
- Phishing tricks people into giving away private info.
- Man-in-the-Middle attacks let bad people read or change messages.
- SQL injection attacks can break databases and let in people who should not be there.
- Zero-Day exploits use problems in software or hardware that no one knows about yet.
- Insider threats come from people who work at the company.
- Advanced Persistent Threats steal data for a long time.
- Distributed Denial of Service attacks flood the network and stop it from working.
- Rogue software looks safe but is actually harmful.
Unauthorized Access
Unauthorized access is when someone joins the network without permission. This can cause stolen data or stop the service. Operators must stop this because it makes the network weak and puts everyone at risk.
Identity Spoofing
Identity spoofing is when someone pretends to be a real user or device. Attackers do this to get into the network or steal information. This makes it hard for operators to know who is real.
Authentication for Risk Mitigation
Authentication helps operators keep their networks safe from these dangers. Strong authentication makes it harder for attackers to get in or pretend to be someone else. Operators use different tools to protect the network.
| Authentication Method | Description |
|---|---|
| RADIUS | A client-server protocol that manages network access and checks who users are. |
| WPA2 | A wireless security protocol that uses AES encryption and 802.1X for authentication. It is safer than WEP. |
Operators use encryption to keep network data safe. This makes it very hard for attackers to read or change information. Access control lists only let approved devices join the network. Port security lets only certain devices connect. These steps help keep the network strong.
- Use encryption to keep network data safe.
- Use access control lists to allow only approved MAC addresses.
- Make port security better by letting only certain MAC addresses connect.
Operators should update their authentication systems often. This helps them find weak spots and stop new attacks.
Regulatory Compliance
Operators must follow rules to keep subscribers and their data safe. These rules explain why operators need strong authentication and data protection. Following these rules helps build trust and keeps the network safe.
| Requirement | Description |
|---|---|
| Secure Authentication | Operators must use safe ways to check customers before SIM changes and number ports. They must review these ways every year. |
| Customer Notification | Providers must tell customers about SIM changes and port-out requests. They must also let customers lock their accounts. |
| Fraud Reporting | Operators must let customers report fraud and must check these reports quickly. |
| CPNI Protection | Operators must have strong rules to stop people from getting customer network information without permission. |
Operators who follow these rules show they care about network safety and privacy. They also avoid fines and legal trouble. Following these rules is not just about the law. It is about keeping the network safe for everyone.
Best Practices for Subscriber Management
Operator Recommendations
Operators need to follow good steps to keep networks safe. These steps help give better internet to homes and businesses. Groups in the industry say operators should do these things:
- Use strong hardware that works well even when many people use it. This keeps the network working during busy times.
- Put towers in the right spots and point antennas the right way. Good placement helps the signal and stops dropped connections.
- Use edge computing to make the network faster for everyone. This lowers delays.
- Use spectrum in a smart way. This stops interference and gives more bandwidth to users.
- Get ready for emergencies with clear plans. Fast action during disasters keeps services working.
- Give clear customer support and self-service tools. These help users fix problems fast and build trust.
- Update software and firmware often. Updates close security holes and stop attacks.
- Work with local groups to reach more people. Partnerships help more people get service and improve it.
Operators do these things to give users a safe and steady connection. Each step helps stop problems before they happen.
Tools and Technologies
Operators use new tools to make managing subscribers easier. Artificial Intelligence (AI) and Machine Learning (ML) are important. These tools help operators find problems early and guess what might go wrong. AI and ML can spot strange patterns in network traffic. This helps operators fix things before users notice. Automation also cuts down on mistakes and saves time. Operators pick these tools to keep the network strong and make things better for every subscriber.
Streamlining Processes
Operators want to work faster and smarter. Automation and AI help them plan better and fix problems quickly. These tools use data to make smart choices about network changes. Operators can use automation to make WiFi better in homes. This matters because most support calls are about WiFi. Real-time tools fix problems as they happen and make sure important devices get the best connection.
Operators can make their work smoother by:
- Using automated steps to plan and set up new connections.
- Making apps easier to use with user interface automation.
- Keeping the network strong with AI and ML for fast problem finding.
Operators who use these good steps can give better service, have less downtime, and keep subscribers happy.
Future Trends in FWA Subscriber Management
Automation and AI
Automation and artificial intelligence are changing how operators manage subscribers. Operators want to know why these tools are important. Automation helps them guess how much traffic will be on the network. This lets them keep things running smoothly. It also makes security better by using resources in a smart way. Operators use automation to fix problems before users notice. This helps customers have a better experience.
Operators pick automation for many reasons. It makes turning on services faster. It helps them handle more users as the network grows. It saves money by making jobs quicker and using online tools. It helps use spectrum in a better way. It also shows how users act and if the network is healthy.
| Aspect | Description |
|---|---|
| Efficient Service Delivery | Automation makes turning on services faster and gives customers a better experience. |
| Operational Scalability | Lets operators handle more users with automated steps. |
| Cost Reduction | Saves money by making jobs easier and using online tools. |
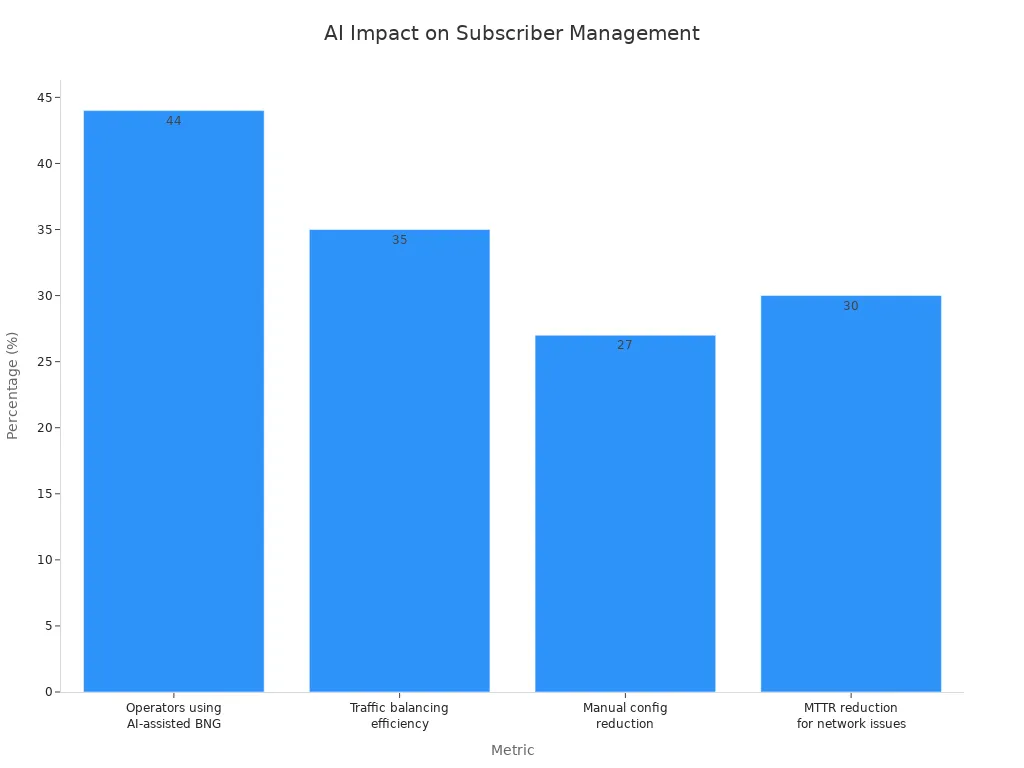
Artificial intelligence adds even more help. Many operators now use AI to help make rules in their networks. AI helps balance traffic, does less manual work, and fixes network problems faster. For example, 44% of operators use AI to help with BNG policy engines. They see a 35% better balance in traffic and a 30% faster fix time for network problems.
Evolving Authentication Standards
Authentication standards in fixed wireless access keep changing. Operators want to know why these changes are important. New standards help stop new security threats. They also make it easier and safer for users to connect. Operators now use stronger encryption and multi-factor authentication. These steps help stop identity spoofing and people getting in without permission.
Operators also want flexible ways to check who is joining. They want systems that work with SIM cards, certificates, and passwords. This helps them serve all kinds of users. As standards change, operators can give safer and more steady connections. They also follow new rules and keep user data safe.
Next-Gen FWA Networks
Next-generation fixed wireless access networks will use more automation and smarter ways to check users. Operators want to know why this is important for the future. These networks will handle more devices and faster data speeds. Automation will help operators manage more subscribers. AI will help them find and fix problems before users notice.
Next-gen networks will also support new things like smart homes and connected cars. Operators will need strong subscriber management to keep these services working well. They will use advanced tools to make sure every user gets the right service and stays safe. As fixed wireless access grows, these trends will help operators give better, faster, and safer internet to everyone.
Good subscriber management and authentication help keep FWA networks safe. Operators who use strong systems protect users and make service better. They also help subscribers trust the network.
- Operators need to:
- Check and change authentication methods often
- Use automation and AI to manage things better
- Follow the best steps in the industry
Learning about new trends helps operators give safer and faster internet. This is why strong management is important for every FWA network.
FAQ
Why do operators need strong subscriber management in FWA networks?
Operators use strong subscriber management to keep the network safe. It helps stop people from getting in without permission. Good management also keeps service quality high. This makes subscribers trust the network.
Why is SIM-based authentication popular in FWA?
SIM-based authentication gives every device its own identity. Operators like this method because it is safe and simple for users. It also helps stop identity spoofing.
Why do operators update authentication systems often?
Operators update authentication systems to block new dangers. These updates help keep the network safe. They also help operators follow security rules. This protects subscriber data.
Why does policy enforcement matter for subscriber experience?
Policy enforcement lets operators control how much data people use. It makes sure everyone gets a fair share. Subscribers get steady and reliable service.
Why do operators use automation and AI in subscriber management?
Automation and AI help operators find problems early. These tools make turning on services faster. They also help the network work better. Operators save time and make fewer mistakes.
Why is certificate-based authentication important for businesses?
Certificate-based authentication uses strong encryption to protect data. Operators pick this for businesses because it keeps important data safe. It also stops devices that should not join.
Why must operators follow regulatory compliance in FWA?
Operators follow regulatory compliance to keep subscriber privacy safe. These rules help stop fraud and protect customer information. Following the rules also keeps operators out of legal trouble.
Why do operators track subscriber usage?
Operators track usage to manage network resources. This helps them offer plans that fit each person. It also helps find strange activity. Usage tracking makes service better.


